
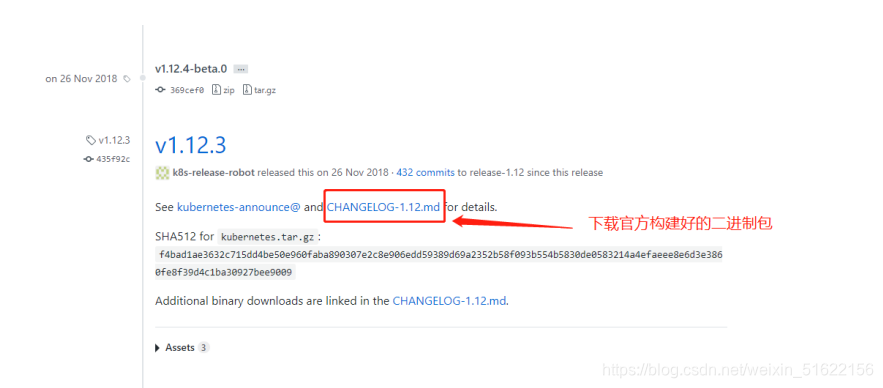
官网地址:https://github.com/kubernetes/kubernetes/releases?after=v1.13.1
Master:192.168.162.10/24 kube-apiserver kube-controller-manager kube-scheduler etcd
Node01:192.168.162.30/24 kubelet kube-proxy docker flannel etcd
Node02:192.168.162.40/24 kubelet kube-proxy docker flannel etcd
[root@localhost ~]# mkdir k8s
[root@localhost ~]# cd k8s/
[root@localhost k8s]# ls //从宿主机拖进来
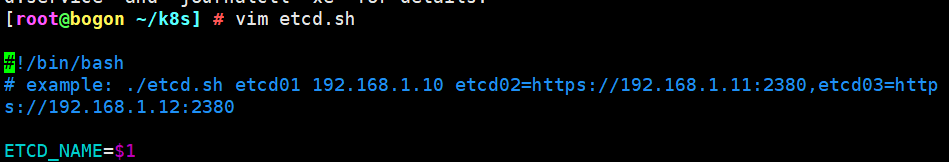
etcd-cert.sh etcd.sh
[root@localhost k8s]# mkdir etcd-cert
[root@localhost k8s]# mv etcd-cert.sh etcd-cert
[root@localhost k8s]# vim cfssl.sh
curl -L https://pkg.cfssl.org/R1.2/cfssl_linux-amd64 -o /usr/local/bin/cfssl
curl -L https://pkg.cfssl.org/R1.2/cfssljson_linux-amd64 -o /usr/local/bin/cfssljson
curl -L https://pkg.cfssl.org/R1.2/cfssl-certinfo_linux-amd64 -o /usr/local/bin/cfssl-certinfo
chmod +x /usr/local/bin/cfssl /usr/local/bin/cfssljson /usr/local/bin/cfssl-certinfo
//下载cfssl官方包
[root@localhost k8s]# bash cfssl.sh
[root@localhost k8s]# ls /usr/local/bin/
cfssl cfssl-certinfo cfssljson
[root@bogon ~/k8s/etcd-cert] # cat > ca-config.json <<EOF
{
"signing": {
"default": {
"expiry": "87600h"
},
"profiles": {
"www": {
"expiry": "87600h",
"usages": [
"signing",
"key encipherment",
"server auth",
"client auth"
]
}
}
}
}
EOF
cat > ca-csr.json <<EOF
{
"CN": "etcd CA",
"key": {
"algo": "rsa",
"size": 2048
},
"names": [
{
"C": "CN",
"L": "Beijing",
"ST": "Beijing"
}
]
}
EOF
cfssl gencert -initca ca-csr.json | cfssljson -bare ca -
2020/01/13 16:32:56 [INFO] generating a new CA key and certificate from CSR
2020/01/13 16:32:56 [INFO] generate received request
2020/01/13 16:32:56 [INFO] received CSR
2020/01/13 16:32:56 [INFO] generating key: rsa-2048
2020/01/13 16:32:56 [INFO] encoded CSR
2020/01/13 16:32:56 [INFO] signed certificate with serial number 595395605361409801445623232629543954602649157326
cat > server-csr.json <<EOF
{
"CN": "etcd",
"hosts": [
"192.168.162.10",
"192.168.162.30",
"192.168.162.40"
],
"key": {
"algo": "rsa",
"size": 2048
},
"names": [
{
"C": "CN",
"L": "BeiJing",
"ST": "BeiJing"
}
]
}
EOF
cfssl gencert -ca=ca.pem -ca-key=ca-key.pem -config=ca-config.json -profile=www server-csr.json | cfssljson -bare server
2020/01/13 17:01:30 [INFO] generate received request
2020/01/13 17:01:30 [INFO] received CSR
2020/01/13 17:01:30 [INFO] generating key: rsa-2048
2020/01/13 17:01:30 [INFO] encoded CSR
2020/01/13 17:01:30 [INFO] signed certificate with serial number 202782620910318985225034109831178600652439985681
2020/01/13 17:01:30 [WARNING] This certificate lacks a "hosts" field. This makes it unsuitable for
websites. For more information see the Baseline Requirements for the Issuance and Management
of Publicly-Trusted Certificates, v.1.1.6, from the CA/Browser Forum (https://cabforum.org);
specifically, section 10.2.3 ("Information Requirements").
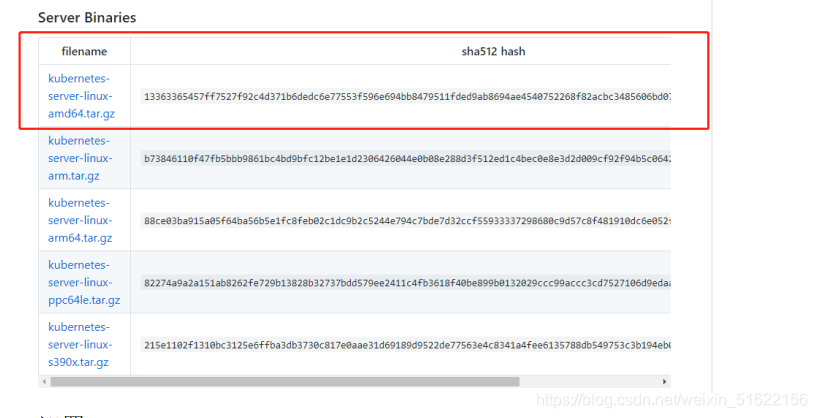
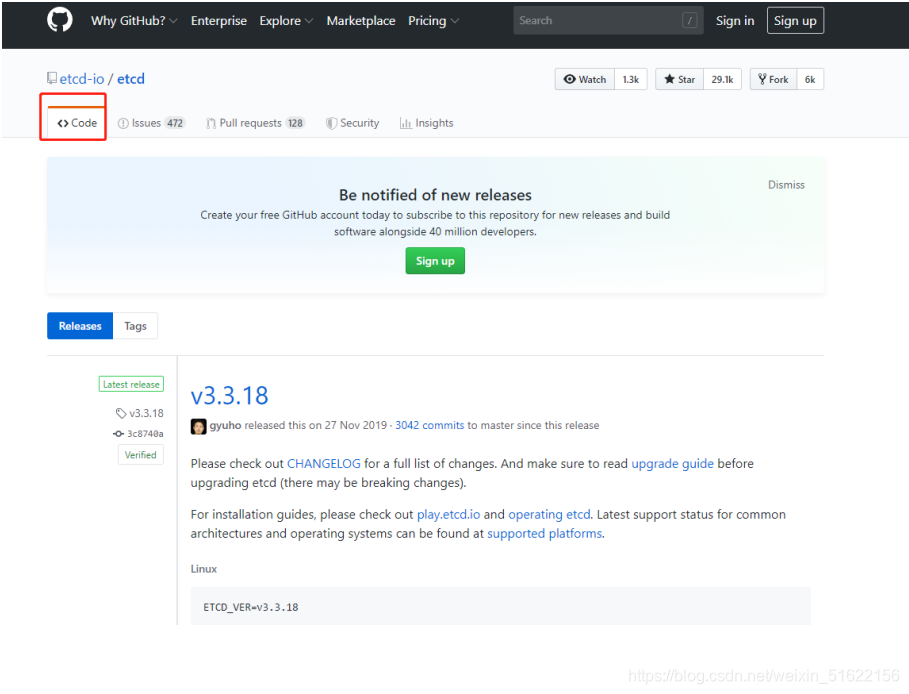
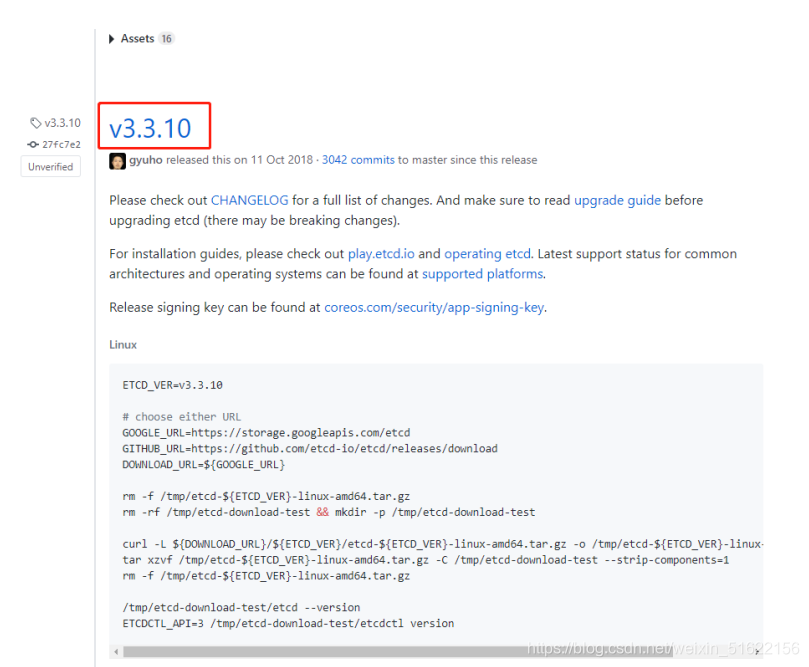
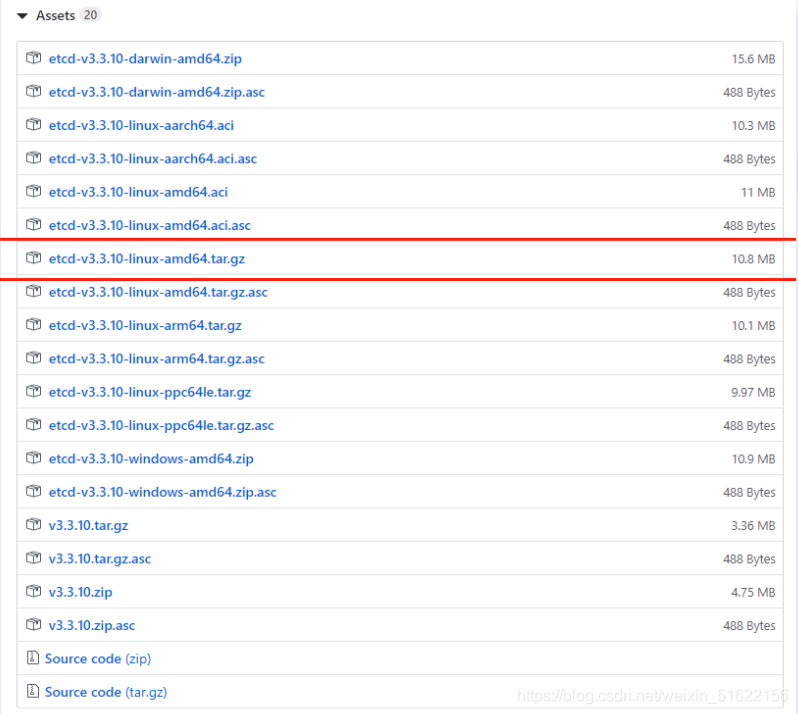
https://github.com/etcd-io/etcd/releases #二进制包地址
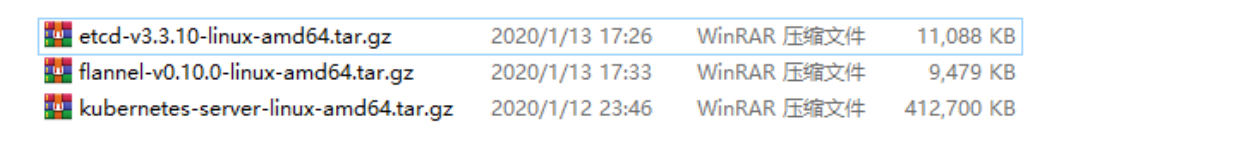
将包复制到centos7中
[root@bogon ~/k8s] # ls
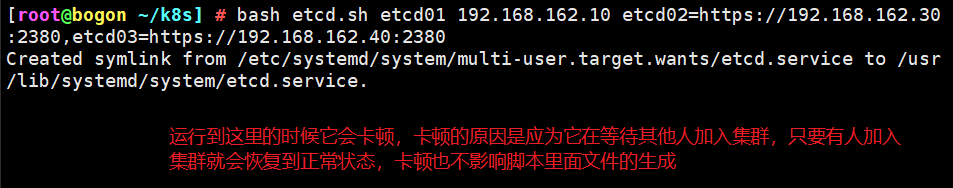
etcd-cert etcd.sh etcd-v3.3.10-linux-amd64.tar.gz
[root@bogon ~/k8s] # tar zxvf etcd-v3.3.10-linux-amd64.tar.gz
[root@localhost k8s]# ls etcd-v3.3.10-linux-amd64
Documentation etcd etcdctl README-etcdctl.md README.md READMEv2-etcdctl.md
[root@localhost k8s]# mkdir /opt/etcd/{cfg,bin,ssl} -p //配置文件,命令文件,证书
[root@localhost k8s]# mv etcd-v3.3.10-linux-amd64/etcd etcd-v3.3.10-linux-amd64/etcdctl /opt/etcd/bin/
[root@localhost k8s]# cp etcd-cert/*.pem /opt/etcd/ssl/
[root@localhost k8s]# scp -r /opt/etcd/ root@192.168.162.30:/opt/
[root@localhost k8s]# scp -r /opt/etcd/ root@192.168.162.40:/opt
[root@localhost k8s]# scp /usr/lib/systemd/system/etcd.service root@192.168.162.30:/usr/lib/systemd/system/
[root@localhost k8s]# scp /usr/lib/systemd/system/etcd.service root@192.168.162.40:/usr/lib/systemd/system/
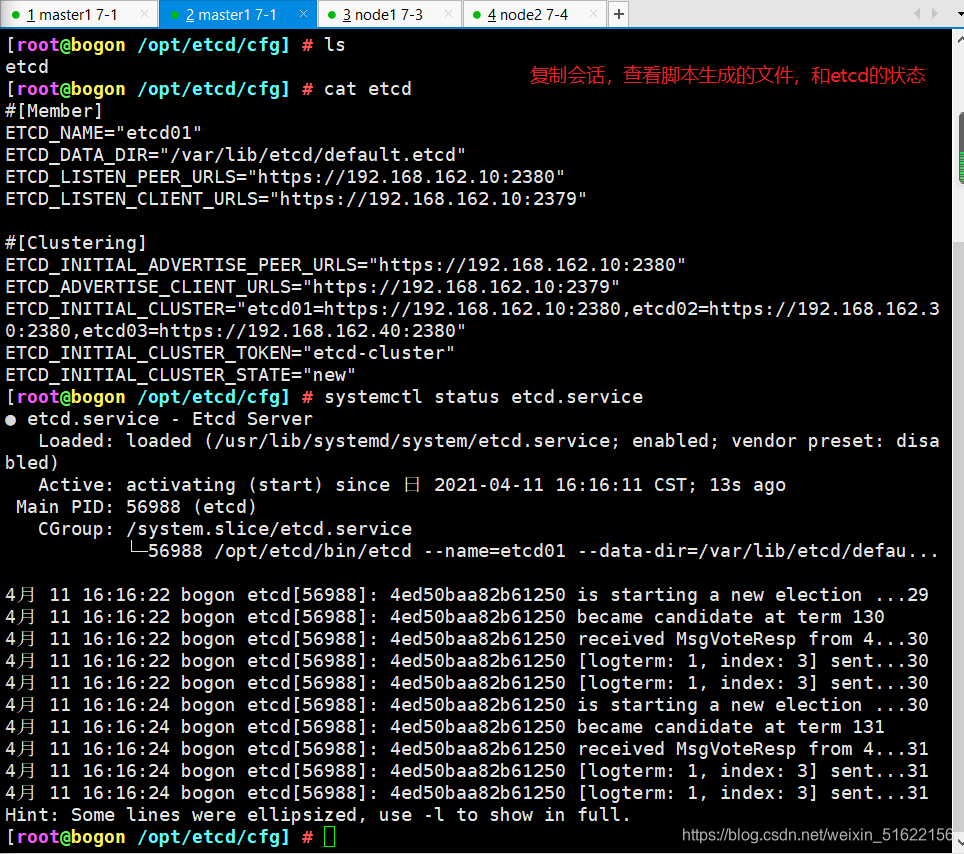
[root@localhost ~]# vim /opt/etcd/cfg/etcd
#[Member]
ETCD_NAME="etcd02"
ETCD_DATA_DIR="/var/lib/etcd/default.etcd"
ETCD_LISTEN_PEER_URLS="https://192.168.162.30:2380"
ETCD_LISTEN_CLIENT_URLS="https://192.168.162.30:2379"
#[Clustering]
ETCD_INITIAL_ADVERTISE_PEER_URLS="https://192.168.162.30:2380"
ETCD_ADVERTISE_CLIENT_URLS="https://192.168.162.30:2379"
ETCD_INITIAL_CLUSTER="etcd01=https://192.168.162.10:2380,etcd02=https://192.168.162.30:2380,etcd03=https://192.168.162.40:2380"
ETCD_INITIAL_CLUSTER_TOKEN="etcd-cluster"
ETCD_INITIAL_CLUSTER_STATE="new"
启动
[root@localhost ssl]# systemctl start etcd
[root@localhost ssl]# systemctl status etcd
#[Member]
ETCD_NAME="etcd03"
ETCD_DATA_DIR="/var/lib/etcd/default.etcd"
ETCD_LISTEN_PEER_URLS="https://192.168.162.40:2380"
ETCD_LISTEN_CLIENT_URLS="https://192.168.162.40:2379"
#[Clustering]
ETCD_INITIAL_ADVERTISE_PEER_URLS="https://192.168.162.40:2380"
ETCD_ADVERTISE_CLIENT_URLS="https://192.168.162.40:2379"
ETCD_INITIAL_CLUSTER="etcd01=https://192.168.162.10:2380,etcd02=https://192.168.162.30:2380,etcd03=https://192.168.162.40:2380"
ETCD_INITIAL_CLUSTER_TOKEN="etcd-cluster"
ETCD_INITIAL_CLUSTER_STATE="new"
启动
[root@localhost ssl]# systemctl start etcd
[root@localhost ssl]# systemctl status etcd
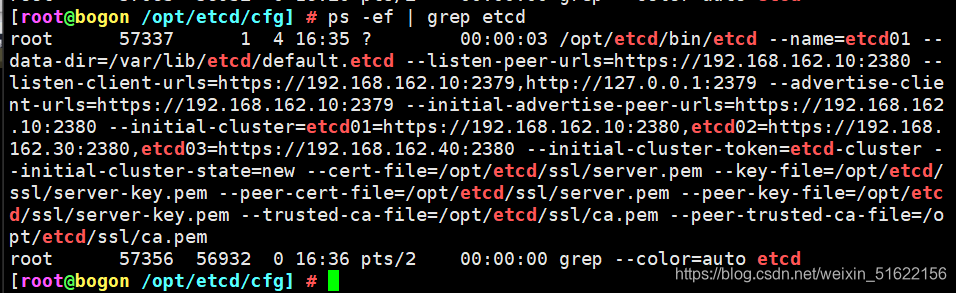
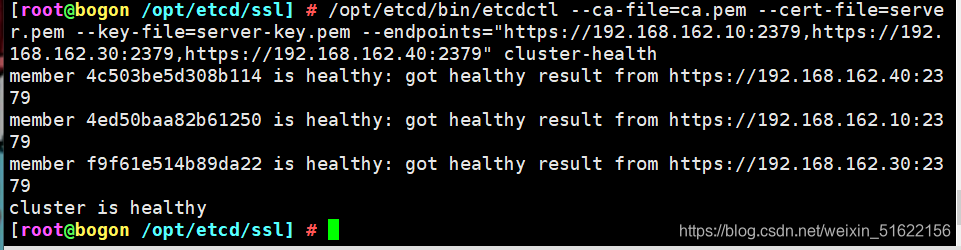
[root@bogon /opt/etcd/ssl] # /opt/etcd/bin/etcdctl --ca-file=ca.pem --cert-file=server.pem --key-file=server-key.pem --endpoints="https://192.168.162.10:2379,https://192.168.162.30:2379,https://192.168.162.40:2379" cluster-health
Elasticsearch 是通过 Lucene 的倒排索引技术实现比关系型数据库更快的过滤。特...
复制代码 代码如下: % URL="http://news.163.com/special/00011K6L/rss_newstop....
工具:Eclipse,Oracle,smartupload.jar;语言:jsp,Java;数据存储:Oracle。...
4月11日20:30~22:00通过腾讯会议进行了第二次在线学习讨论我把学习笔记整理一下...
错误描述: 在开发.net项目中,通过microsoft.ACE.oledb读取excel文件信息时,报...
上篇文章给大家介绍了 Java正则表达式匹配,替换,查找,切割的方法 ,接下来,...
正则忽略大小写 – RegexOptions.IgnoreCase 例如: 复制代码 代码如下: Str = R...
DELETEFROMTablesWHEREIDNOTIN(SELECTMin(ID)FROMTablesGROUPBYName) Min的话保...
本文实例讲述了Laravel框架源码解析之反射的使用。分享给大家供大家参考,具体如...
项目中用到的一些特殊字符和图标 html代码 XML/HTML Code 复制内容到剪贴板 div ...