
Minikube是-一个工具,可以在本地快速运行一-个单点的Kubernetes,仅用于尝试Kubernetes或日常开发的用户使用。
部署地址: https://kubernetes.io/docs/setup/minikube/
Kubeadm也是一一个 工具,提供kubeadm init和kubeadm join,用于快速部署Kubernetes集群。部署地址:
https://kubernetes.io/docs/reference/setup-tools/kubeadm/kubeadm/
推荐,从官方下载发行版的二进制包,手动部署每个组件,组成Kubernetes集群。下 载地址:
https://github.com/kubernetes/kubernetes/releases
环境部署
官网地址:https://github.com/kubernetes/kubernetes/releases?after=v1.13.1

K8S部署
Master:192.168.177.33/24 kube-apiserver kube-controller-manager kube-scheduler etcd
Node01:192.168.177.8/24 kubelet kube-proxy docker flannel etcd
Node02:192.168.177.18/24 kubelet kube-proxy docker flannel etcd
master操作
[root@localhost ~]# mkdir k8s
[root@localhost ~]# cd k8s/
[root@localhost k8s]# ls //从宿主机拖进来
etcd-cert.sh etcd.sh
[root@localhost k8s]# mkdir etcd-cert
[root@localhost k8s]# mv etcd-cert.sh etcd-cert
下载证书制作工具
[root@localhost k8s]# vim cfssl.sh
curl -L https://pkg.cfssl.org/R1.2/cfssl_linux-amd64 -o /usr/local/bin/cfssl
curl -L https://pkg.cfssl.org/R1.2/cfssljson_linux-amd64 -o /usr/local/bin/cfssljson
curl -L https://pkg.cfssl.org/R1.2/cfssl-certinfo_linux-amd64 -o /usr/local/bin/cfssl-certinfo
chmod +x /usr/local/bin/cfssl /usr/local/bin/cfssljson /usr/local/bin/cfssl-certinfo
下载证书制作工具
[root@master1 k8s]# bash cfssl.sh
[root@master1 k8s]# ls /usr/local/bin/
cfssl cfssl-certinfo cfssljson
下载cfssl官方包
[root@master1 k8s]# bash cfssl.sh
[root@master1 k8s]# ls /usr/local/bin/
cfssl cfssl-certinfo cfssljson
开始制作证书
//cfssl 生成证书工具 , cfssljson通过传入json文件生成证书,cfssl-certinfo查看证书信息
定义ca证书
[root@master1 ~]# cd /root/k8s/etcd-cert
cat > ca-config.json <<EOF
{
"signing": {
"default": {
"expiry": "87600h"
},
"profiles": {
"www": {
"expiry": "87600h",
"usages": [
"signing",
"key encipherment",
"server auth",
"client auth"
]
}
}
}
}
EOF
实现证书签名
[root@master1 ~]# cd /root/k8s/etcd-cert
cat > ca-csr.json <<EOF
{
"CN": "etcd CA",
"key": {
"algo": "rsa",
"size": 2048
},
"names": [
{
"C": "CN",
"L": "Beijing",
"ST": "Beijing"
}
]
}
EOF
生产证书,生成ca-key.pem ca.pem
[root@master1 etcd-cert]# cfssl gencert -initca ca-csr.json | cfssljson -bare ca -
2021/04/12 22:53:30 [INFO] generating a new CA key and certificate from CSR
2021/04/12 22:53:30 [INFO] generate received request
2021/04/12 22:53:30 [INFO] received CSR
2021/04/12 22:53:30 [INFO] generating key: rsa-2048
2021/04/12 22:53:30 [INFO] encoded CSR
2021/04/12 22:53:30 [INFO] signed certificate with serial number 397125830926114737701706075410049927608256756699
指定etcd三个节点之间的通信验证
[root@master1 ~]# cd /root/k8s/etcd-cert
cat > server-csr.json <<EOF
{
"CN": "etcd",
"hosts": [
"192.168.177.33",
"192.168.177.8",
"192.168.177.18"
],
"key": {
"algo": "rsa",
"size": 2048
},
"names": [
{
"C": "CN",
"L": "BeiJing",
"ST": "BeiJing"
}
]
}
EOF
生成ETCD证书 server-key.pem server.pem
[root@master1 ~]# cd /root/k8s/etcd-cert
[root@master1 etcd-cert]# cfssl gencert -ca=ca.pem -ca-key=ca-key.pem -config=ca-config.json -profile=www server-csr.json | cfssljson -bare server
2021/04/12 22:57:45 [INFO] generate received request
2021/04/12 22:57:45 [INFO] received CSR
2021/04/12 22:57:45 [INFO] generating key: rsa-2048
2021/04/12 22:57:45 [INFO] encoded CSR
2021/04/12 22:57:45 [INFO] signed certificate with serial number 219342381748991728851284184667512408378336584859
2021/04/10 22:57:45 [WARNING] This certificate lacks a "hosts" field. This makes it unsuitable for
websites. For more information see the Baseline Requirements for the Issuance and Management
of Publicly-Trusted Certificates, v.1.1.6, from the CA/Browser Forum (https://cabforum.org);
specifically, section 10.2.3 ("Information Requirements").
[root@master1 etcd-cert]# ls
ca-config.json ca-key.pem server.csr server.pem
ca.csr ca.pem server-csr.json
ca-csr.json etcd-cert.sh server-key.pem
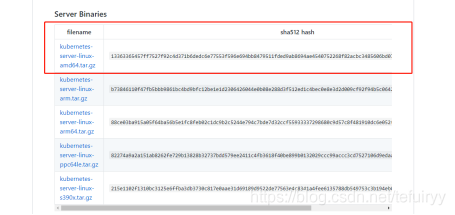
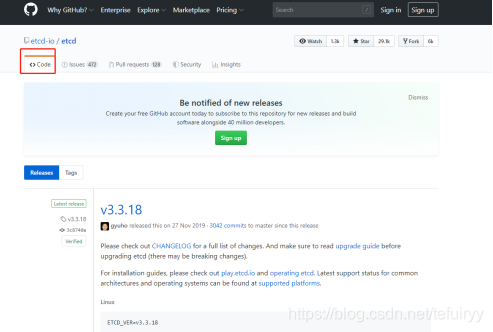
ETCD二进制包地址
https://github.com/etcd-io/etcd/releases
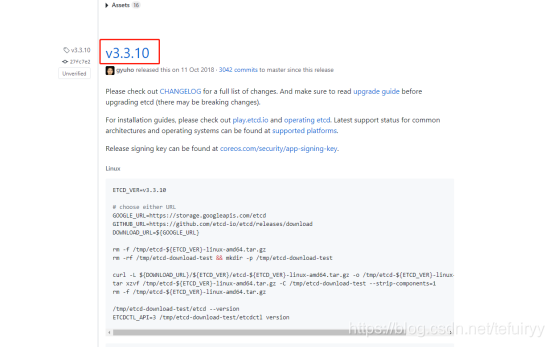
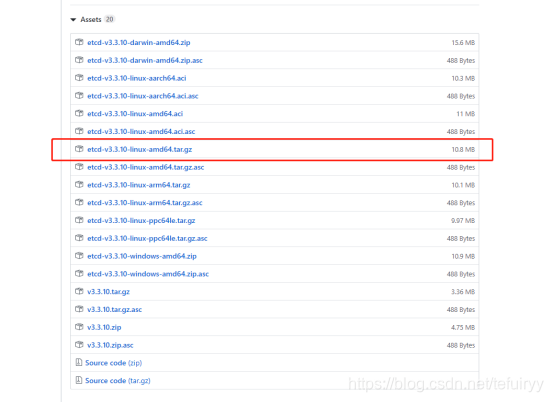
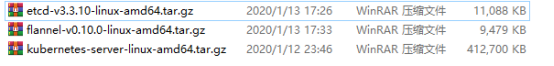
将以上三个压缩包上传到 /root/k8s目录中
[root@master1 etcd-cert]# cd ~/k8s/
[root@master1 k8s]# ls
cfssl.sh etcd.sh flannel-v0.10.0-linux-amd64.tar.gz
etcd-cert etcd-v3.3.10-linux-amd64.tar.gz kubernetes-server-linux-amd64.tar.gz
[root@master1 k8s]# tar zxvf etcd-v3.3.10-linux-amd64.tar.gz
[root@master1 k8s]# ls etcd-v3.3.10-linux-amd64
Documentation etcdctl README.md
etcd README-etcdctl.md READMEv2-etcdctl.md
[root@master1 k8s]# mkdir /opt/etcd/{cfg,bin,ssl} -p //cfg:配置文件,bin:命令文件,ssl:证书
[root@master1 k8s]# mv etcd-v3.3.10-linux-amd64/etcd etcd-v3.3.10-linux-amd64/etcdctl /opt/etcd/bin/
[root@master1 k8s]# ls /opt/etcd/bin/
etcd etcdctl
证书拷贝
[root@master1 k8s]# cp etcd-cert/*.pem /opt/etcd/ssl/
[root@master1 k8s]# ls /opt/etcd/ssl/
ca-key.pem ca.pem server-key.pem server.pem
进入卡住状态等待其他节点加入
[root@master1 k8s]# bash etcd.sh etcd01 192.168.177.33 etcd02=https://192.168.177.8:2380,etcd03=https://192.168.177.18:2380
新开master1的一个会话,会发现etcd进程已经开启
[root@localhost ~]# ps -ef | grep etcd
拷贝证书去其他节点
[root@master1 k8s]# scp -r /opt/etcd/ root@192.168.177.8:/opt/
[root@master1 k8s]# scp -r /opt/etcd/ root@192.168.177.18:/opt/
启动脚本拷贝其他节点
[root@master1 ~]# scp /usr/lib/systemd/system/etcd.service root@192.168.177.8:/usr/lib/systemd/system/
[root@master1 ~]# scp /usr/lib/systemd/system/etcd.service root@192.168.177.18:/usr/lib/systemd/system/
在node1节点与node2节点均需修改
###在node1节点修改
[root@node1 system]# cd /opt/etcd/cfg/
[root@node1 cfg]# vim etcd
#[Member]
ETCD_NAME="etcd02"
ETCD_DATA_DIR="/var/lib/etcd/default.etcd"
ETCD_LISTEN_PEER_URLS="https://192.168.177.8:2380"
ETCD_LISTEN_CLIENT_URLS="https://192.168.177.8:2379"
#[Clustering]
ETCD_INITIAL_ADVERTISE_PEER_URLS="https://192.168.177.8:2380"
ETCD_ADVERTISE_CLIENT_URLS="https://192.168.177.8:2379"
ETCD_INITIAL_CLUSTER="etcd01=https://192.168.177.33:2380,etcd02=https://192.168.177.8:2380,etcd03=https://192.168.177.18:2380"
ETCD_INITIAL_CLUSTER_TOKEN="etcd-cluster"
ETCD_INITIAL_CLUSTER_STATE="new"
###在node2节点修改
[root@node2 system]# cd /opt/etcd/cfg/
[root@node2 cfg]# vim etcd
#[Member]
ETCD_NAME="etcd03"
ETCD_DATA_DIR="/var/lib/etcd/default.etcd"
ETCD_LISTEN_PEER_URLS="https://192.168.177.18:2380"
ETCD_LISTEN_CLIENT_URLS="https://192.168.177.18:2379"
#[Clustering]
ETCD_INITIAL_ADVERTISE_PEER_URLS="https://192.168.177.18:2380"
ETCD_ADVERTISE_CLIENT_URLS="https://192.168.177.18:2379"
ETCD_INITIAL_CLUSTER="etcd01=https://192.168.177.33:2380,etcd02=https://192.168.177.8:2380,etcd03=https://192.168.177.18:2380"
ETCD_INITIAL_CLUSTER_TOKEN="etcd-cluster"
ETCD_INITIAL_CLUSTER_STATE="new"
启动
#首先在master1节点上进行启动
[root@master1 ~]# cd /root/k8s/
[root@master1 k8s]# bash etcd.sh etcd01 192.168.177.33 etcd02=https://192.168.177.8:2380,etcd03=https://192.168.177.18:2380
#接着在node1和node2节点分别进行启动
[root@node1 cfg]# systemctl start etcd.service
[root@node2 cfg]# systemctl start etcd.service
检查群集状态,在master1上进行检查
[root@master1 ~]# cd /root/k8s/etcd-cert/
[root@master1 etcd-cert]# /opt/etcd/bin/etcdctl --ca-file=ca.pem --cert-file=server.pem --key-file=server-key.pem --endpoints="https://192.168.177.33:2379,https://192.168.177.8:2379,https://192.168.177.18:2379" cluster-health
member 995575c0c650e89b is healthy: got healthy result from https://192.168.177.8:2379
member 9abd0b70bb7a8d9a is healthy: got healthy result from https://192.168.177.33:2379
member acca2e49c9c76117 is healthy: got healthy result from https://192.168.177.18:2379
cluster is healthy
详情看这里 http://hi.baidu.com/lael80/blog/item/6633d7fc89f9f282b801a061.ht...
今天写个jsp页面,乍么调来调去div style=margin:0 auto123xxx/div 这个属怎么弄...
php将字符串转换为数组 在php中通过使用“explode函数”,将字符串转换为数组,...
adb shell的功能很强大,可以使用很多功能,今天我们说下通过控制按键输入:adb ...
橡皮擦一个逗趣的互联网高级网虫。新的系列让我们一起进入 Django 世界。 已经完...
github常用命令 最近开始研究github,mark下一些常用命令 git remote add upstre...
1、新建DLL 打开VB6--文件--新建工程--选择ActiveX DLL--确定 2、将默认工程、类...
阅读目录 正则表达式的创建 正则表达式中的特殊字符 \ (反斜杠) ^ $ *, +, .(小...
'************************************* 'asp计算随机数 '********************...
Spring Security缓存的应用之登陆后跳转到登录前源地址 什么意思? 用户访问网站...